Blog
Windows 11 Will No Longer Trust Old Drivers by Default Under New Kernel Policy
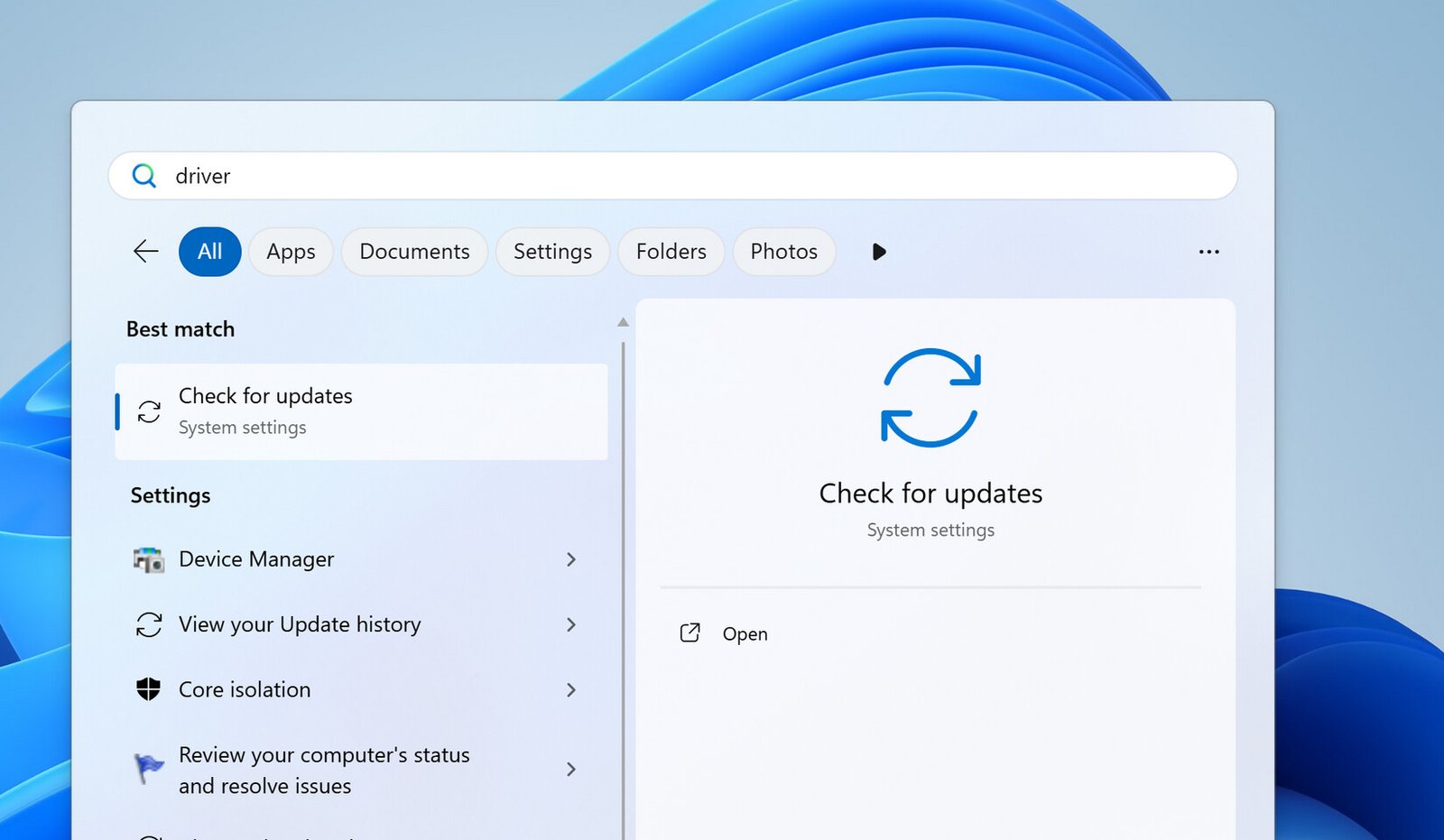
The WHCP will ensure that each driver receives a valid security certificate that meets Microsoft’s security standards. This update will be implemented with OS versions Windows 11 24H2, 25H2, 26H1, Windows Server 2025, and future releases. Despite this change, Microsoft will still allow Windows to load older, trusted drivers to maintain backward compatibility and its long-standing plug-and-play feature. The April 2026 Windows update will begin enforcing the new policy in evaluation mode on supported systems. During this period, Windows will monitor driver activity and only fully activate the policy once it determines that doing so will not cause compatibility issues. Microsoft is also maintaining a curated allow list of reputable cross-signed drivers, ensuring that widely used software and hardware can continue to function where necessary, easing the transition.
For environments that still require custom kernel drivers, Microsoft offers an alternative through Application Control for Business, formerly known as WDAC. This option is designed for confidential or internal-only driver scenarios, allowing organizations to approve privately signed code through policies linked to Secure Boot trust anchors such as the Platform Key or Key Exchange Key. In essence, Microsoft is attempting to balance security and compatibility while encouraging the Windows ecosystem to adopt WHCP-certified drivers as the standard moving forward.