Blog
Emerging tools and techniques for secure hardware design
Designing secure hardware is no longer an elective specialty; it is a core requirement for any modern SoC, but identifying and mitigating hardware-level vulnerabilities demands a robust ecosystem of specialized tools and rigorous architectural principles.
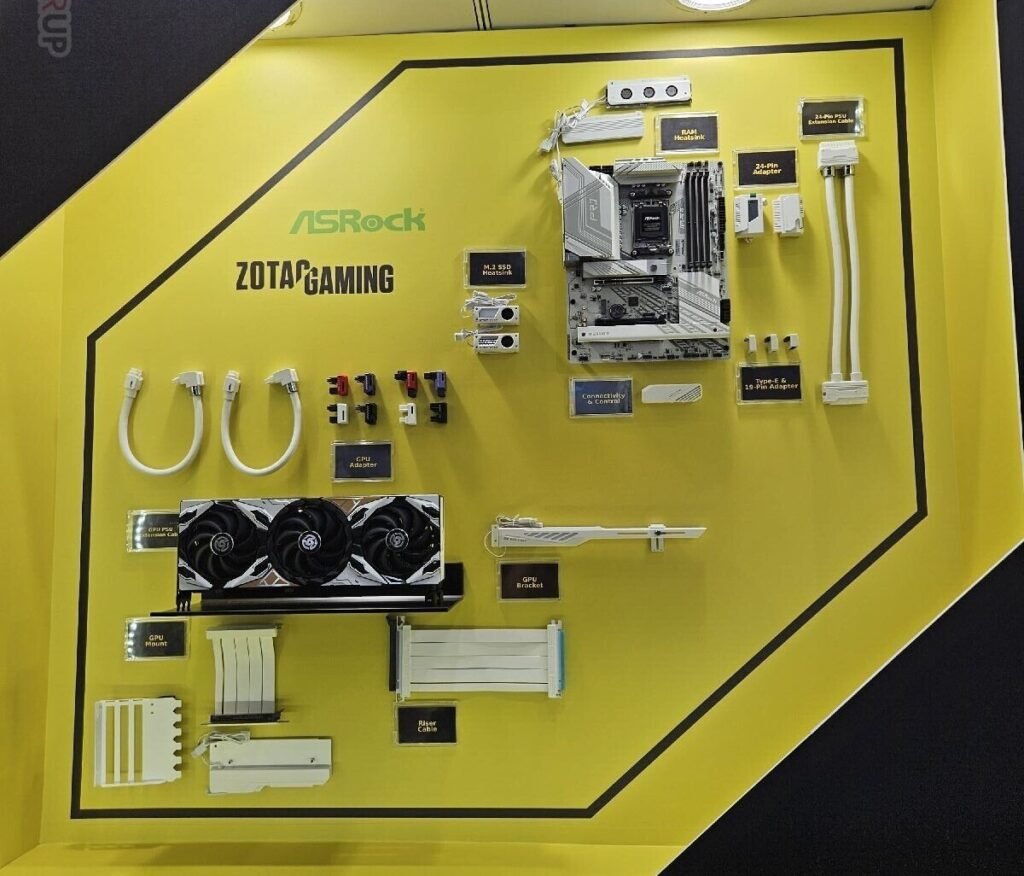
Figure 1: Silicon root of trust: embedding security at the foundation. (Source: Adobe AI Generated)
This article provides a deep dive into the practical arsenal available to today’s hardware engineers. We will analyse the essential tools and architectural techniques, such as hardware-based enclaves and formal verification, that enable engineers to safeguard intellectual property and sensitive data within the chip.
Secure architecture techniques
A hardware root of trust (HRoT) serves as the system’s foundational, immutable source of trust. Implemented directly in silicon – via a secure boot ROM or a dedicated security controller – it executes critical functions such as digital signature verification and cryptographic key management. Its primary objective is to ensure that only authentic, untampered code runs from the moment of power-on, establishing a reliable chain of trust.
Trusted execution environments (TEEs) create a secure enclave within the processor, logically and physically partitioned from the main operating system (Rich OS). By isolating hardware resources, a TEE protects sensitive data and critical algorithm execution even if the primary OS kernel is compromised. Industry standards such as Arm TrustZone or Intel SGX leverage this architecture to handle biometric data and secure payment processing within a protected environment.
Side-channel mitigation involves counter measures focused on blocking the unintentional leakage of information through physical hardware signals. Designers implement specific logic to prevent attackers from deducing cryptographic keys by analyzing power consumption, electromagnetic emissions, or timing variations during processing. Key techniques include constant-time programming, power-load balancing, and the insertion of random noise or jitter into critical operations.
Design tools and frameworks
Caliptra is an open-source root of trust specification designed to be integrated into SoCs as a reusable IP block. Its standardised architecture ensures secure boot and transparent hardware identity, eliminating the opacity of proprietary solutions.
Formal verification tools use rigorous mathematical methods to prove that a chip design strictly complies with its security specifications. Unlike traditional simulation testing, formal verification analyses all possible system states to identify critical vulnerabilities, such as side-channel attacks or information leaks, before the silicon goes to production.
CAD for security represents a new generation of computer-aided design tools that integrate protection metrics into the standard development flow. These utilities allow engineers to automate the insertion of countermeasures – such as logic obfuscation or hardware Trojan detection – ensuring that security is as high a design priority as power consumption or performance.
Emerging trends
With the advance of quantum computing, traditional encryption algorithms are at risk. Hardware implementation of post-quantum cryptography (PQC) focuses on integrating cryptographic accelerators capable of executing quantum-resistant algorithms, such as lattice-based ones. The challenge for designers is to incorporate these functions without compromising power efficiency or chip area, ensuring that current devices remain secure in the post-quantum era.
Supply chain security is a trend that addresses hardware integrity from manufacturing to final delivery. In response to threats such as chip recycling, counterfeiting, or the insertion of hardware trojans during manufacturing, techniques like physical unclonable functions (PUFs) and blockchain tracking are being implemented. These tools create a unique ‘digital fingerprint’ for each chip, ensuring that the hardware is authentic and has not been tampered with by malicious actors.
Figure 2: Accelerating security: the rise of specialised hardware modules. (Source: Unsplash)
Design constraints and implementation challenges
While these security techniques are robust in theory, electronic engineers must navigate significant trade-offs during the implementation phase:
Implementing a hardware root of trust and TEE-based isolation requires dedicated silicon real-time, directly impacting the PPA (power, performance and area) metrics of the design. This integration increases the total gate count and power consumption, which can be a critical deal-breaker for battery-powered IoT devices or area-constrained asics where every square millimeter of silicon is at a premium.
Securing a chip increases the verification surface exponentially. Standard EDA tools are often optimised for functional correctness, not for detecting subtle information leaks. Engineers must employ specialised formal verification and side-channel analysis tools, which can significantly extend the time-to-market.
Toward a security-first hardware design
The transition from software-defined security to silicon-based trust is no longer a strategic choice but a technical necessity. Integrating architectures like HRoT and TEEs – while managing the inevitable PPA trade-offs – is the only viable path to protecting the global supply chain and sensitive data in the post-quantum era. For the modern electronic engineer, the challenge lies in mastering this new generation of EDA and formal verification tools to ensure that security is baked into the RTL, not added as an afterthought. Ultimately, a robust, unified hardware-level defense is the only foundation upon which a truly resilient digital ecosystem can be built.
AGI is coming but poses new cybersecurity dilemmas