Blog
As infrastructure becomes smarter, so does cybersecurity

Smart technology infrastructure, such as smart cities and smart grids, brings the physical and digital worlds together. However, the implementation of digitally connected hardware brings a lot of challenges on the digital side because many ‘nodes’ in the smart network (sensors, inverters, smart meters and other digitally connected technologies) are often unsecured, lack robust cybersecurity protocols and are not standardised between manufacturers.
Cybersecurity challenges
Digitally connected devices are critical for the implementation of smart networks. However, there are a lot of potential entry points for hackers to exploit. This is compounded by the majority of the devices being IoT devices, such as IoT-enabled sensors and control systems that lack encryption. With no standardisation firmly in place, both robust and non-robust devices are entering the market. Standards and regulations are starting to come into place, but there is still work to be done.
The more devices that remain unsecured, the more vulnerable smart networks are to attacks as there is a bigger ‘attack surface’ for hackers to exploit. The risk in many smart networks is compounded by these networks running on cloud computing architecture. While there are many security layers to cloud computing architecture, the exploitation from a node can give hackers the potential to cause damage or chaos with that node. It is also possible that the hackers will have a much easier route into the whole network using the node as a gateway — which may contain sensitive data on customers, or gives access to the control of critical infrastructure.
Smart city networks are at risk from a range of attacks, including man-in-the-middle, data theft, device hijacking, distributed denial of service (DDoS) and permanent denial of service (PDoS). While man-in-the-middle attacks can target utility communication networks individual devices can be hijacked, giving control and the ability to enter the wider network to the hacker. Data theft could result in personal information being collected from surveillance cameras leading to identify theft. DDoS attacks can take over different assets so that they can become part of a botnet for targeting more critical infrastructure and PDoS attacks could permanently take out hardware.
The use of AI can be used to make it easier to plan and implement cyberattacks and to perform attacks when hackers have less data at their disposal. AI also makes it easier for less technically competent hackers to perform cyberattacks as the AI can do all the ‘heavy lifting’ by finding network vulnerabilities and reducing the time required to co-ordinate an attack. One of the biggest risks could be AI-driven malware, as these viruses have the potential to adapt to the system to evade attack and seek out high-value targets in the network.
Protecting smart cities
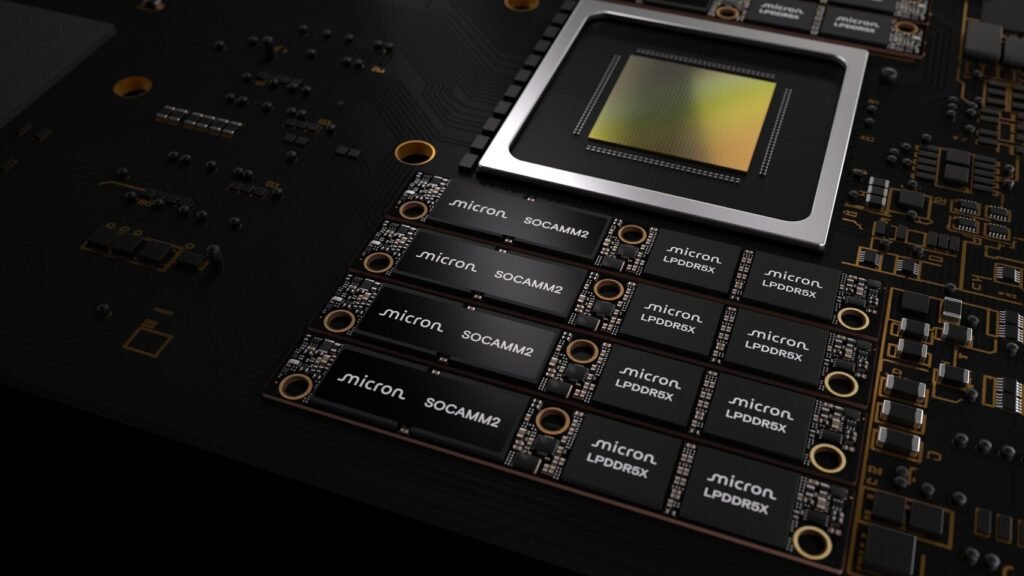
Smart city infrastructure contains three critical layers: a massive hardware network composed of sensors, control systems, communication networks and other small devices; a software layer that analyses the data obtained by the hardware layer; and the human layer. There are millions of hardware devices in smart city networks, so many protocols need to be implemented and all the systems need to have interoperability with each other to work seamlessly.
As each device comes from different company, all with their own levels of security and update mechanisms, it creates a challenging cybersecurity environment. Many IoT devices are deployed with default passwords, which makes them very vulnerable. Moreover, most of the IoT devices are located in public areas, so physically accessible to potential attackers. This means physical security measures are required alongside digital security protocols. Network segmentation is a critical approach for separating different smart city services into their own network, which allows any potential attacks (or physical devices) to be isolated without affecting the whole network. Secure and end-to-end encrypted communication protocols, encrypted backup procedures, network access management and certificate-based authentication are also key approaches that are vital in smart city cyberdefence.
On the other hand, advanced firewalls with deep packet inspection, zero-trust architecture, intrusion detection systems that can track patterns, traffic filtering systems that can block malicious traffic and cloud-based DDoS mitigation for deflecting attack traffic, are all frontline cybersecurity protocols that are being implemented.
All devices in the network — from IoT devices to portable electronics — need to be integrated with advanced threat detection capabilities and possess two-factor authentication. This relies on personal decisions and human willingness to implement them and keep up to date. IoT devices should not only meet security standards and certification requirements (once fully established) but they need to be made physically tamper-resistant and mounted where they are not easily removable. All devices will need to be updated and patched quickly, which will require a co-ordinated deployment of security updates to ensure that no new vulnerabilities are created from missed updates.
Smart grid infrastructure at risk
“Grid cybersecurity is getting more important, because cybersecurity attacks to the grid can make a huge impact to everyone’s real life” says Daniel Kim, co-founder and chief business officer at Autocrypt. “Smart metering provides data collection for electric power usages of houses, buildings, and factories, including EV chargers and the solar power systems. Almost all the grid operations are based on the smart metering with several technical levels, so the integrity and protection of the collected data is very important for smart grids,” he adds.
Smart meters are a key part of advanced metering infrastructure but they are vulnerable to electricity theft that affects both energy suppliers and customers. False consumption readings can have wider implications in the grid as they will affect the load forecasting accuracy of the smart grid and in turn, reduce grid reliability.
Kim believes that the smart meter challenges are getting more severe, because “for cybersecurity reasons, smart meters usually have limited access. However, many smart meters are now also located in open spaces with EV chargers. So, the attack path is being widened.”
The IoT sensors used to monitor various grid hardware and load conditions are also at risk, as are the supervisory and data acquisition control system. The inverters connecting solar cells to the grid are also at risk due to how many solar cells have been deployed and the fact that they are not very robust devices.
Smart grids are a particularly tricky part of smart city infrastructure to manage because swift action is required due to the criticality of the equipment. Additionally, a lot of legacy equipment is now being upgraded to be digitally connected, but the IoT systems retrofitted to legacy equipment are often implemented with limited IT protocols in place. Common cyber-prevention methods, such as installing patches and rebooting systems is not feasible, nor is it possible to temporarily take out some of the systems as shutting down these systems will affect electricity supply.
For protecting smart grids, Kim tells Electronics Weekly that “for the cybersecurity of smart metering, there are several global standards. One of them is the cybersecurity feature defined by DLMS/COSEM, which requires encryption and authentication for the secure communications based on the keys.” However, he adds: “I am not sure, however, whether actual implementation can guarantee the secure communication and protection for the grid operators. Actual smart meters should be validated in terms of cybersecurity and actual keys should be protected from the smart meter manufacturers. However, smart meters are not expensive devices so they can have some vulnerabilities”.
Looking to the future
Security in smart city environments is a complex cybersecurity challenges and requires multiple protocols being implemented by many different parties. Successful implementation will balance factors from ensuring public safety to safeguarding data privacy, managing risk and fostering continued innovation, and will have to balance urban development with technology design.
With AI also being a potential approach to making hacking easier, we could well see situations in the future where smart cities are being attacked and defended by AI — an AI-on-AI fight. Secure by design protocols are starting to be implemented for different IoT devices to ensure that any security flaws are caught and fixed. However, for this approach to be implemented across the board, it will require more formal certification frameworks. The next generation of smart technology will require more collaboration between manufacturers and governments, but cities that continually invest in robust cybersecurity systems will be the ones that will benefit the most.
See AGI is coming but poses new cybersecurity dilemmas | Electronics Weekly